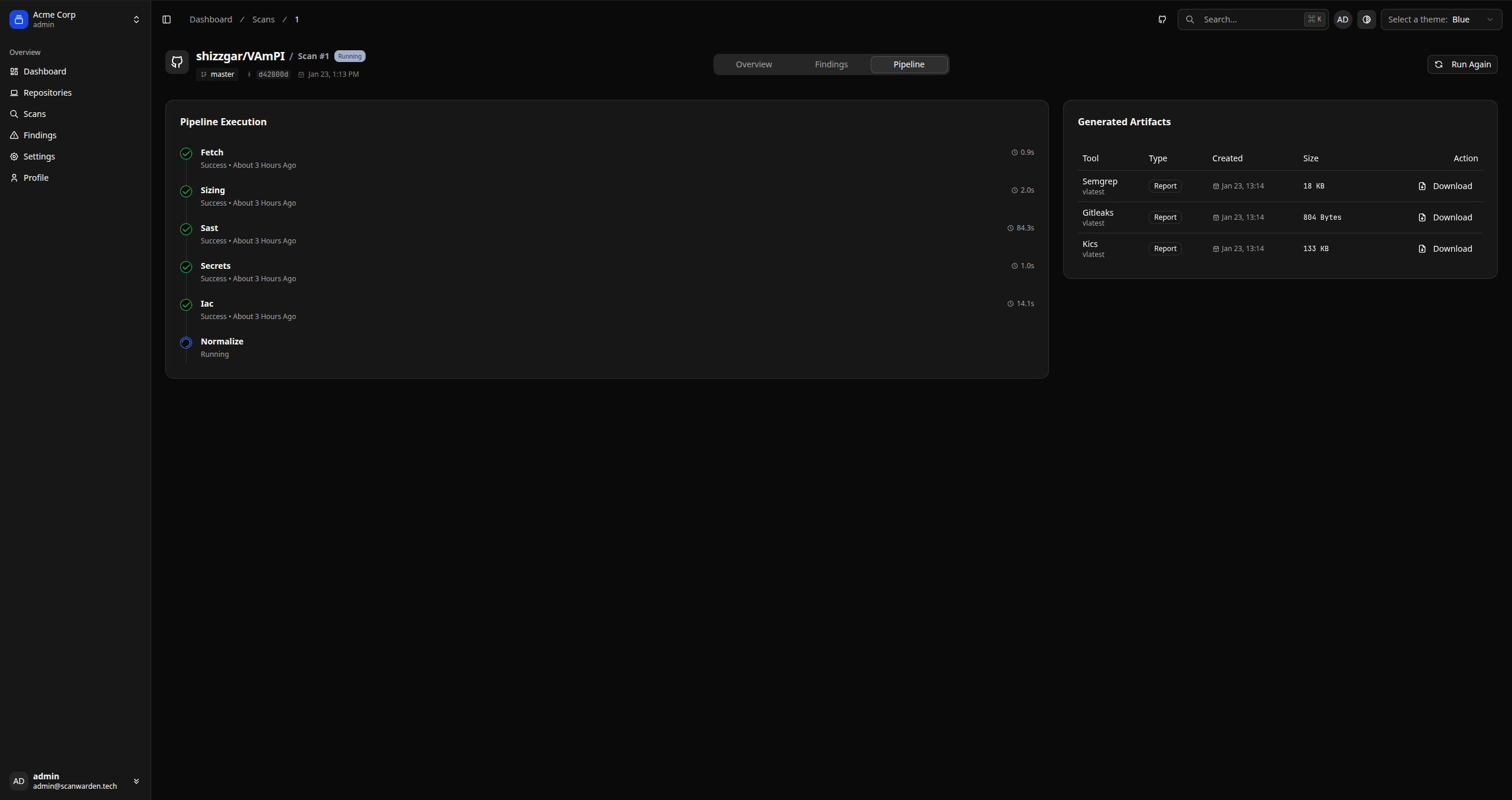
Scanning Pipeline
Supported engines and execution modes
ScanWarden orchestrates open-source security tools in ephemeral, unprivileged containers. This ensures that your code is analyzed securely without dependencies conflicting with each other.
Supported Engines
We currently support the following engines out of the box:
| Category | Tool | Description |
|---|---|---|
| SAST | Opengrep | Static analysis for finding bugs and vulnerabilities. Previously known as Semgrep. |
| Secrets | Gitleaks | Detects hardcoded secrets, keys, and tokens in git history. |
| IaC | KICS | Security checks for Infrastructure as Code (Terraform, Docker, Helm, Kubernetes). |
| Sizing | SCC | Counts lines of code (LOC) and complexity metrics for billing calculation. |
Scan Modes
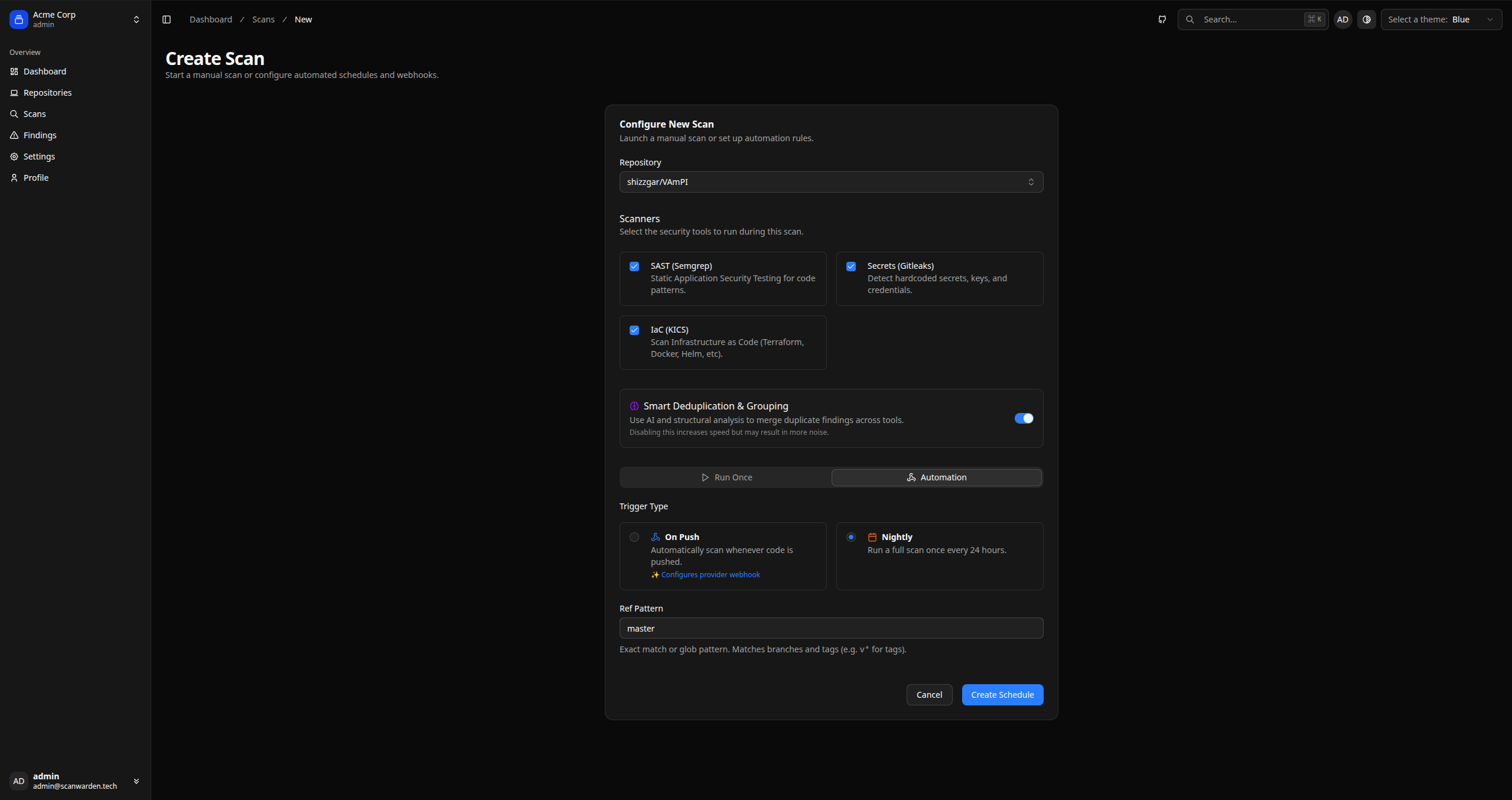
1. Manual Scan
Triggered by a user from the UI for a specific branch and commit. Useful for ad-hoc checks or re-scanning after a fix.
2. Push / Webhook
Automatically triggered when code is pushed to a connected repository. Trigger patterns can be configured.
3. Nightly (Scheduled)
Runs once every 24 hours on the default branch. Trigger patterns can be configured.